Key Takeaways
- IT services for manufacturing help reduce downtime, protect uptime, and keep critical production systems running smoothly.
- They improve visibility across networks, devices, applications, and integrations that support modern manufacturing operations.
- Strong support models help manufacturers secure IT/OT environments, manage vendor access, and reduce operational risk.
- Standardized IT practices across plants, shifts, and sites make it easier to scale, support teams, and maintain consistency.
- A well-managed approach combines monitoring, recovery planning, and continuous improvement to strengthen long-term resilience.
Introduction
Modern plants run on interconnected systems—ERP and MES workflows, shop-floor networks, industrial PCs, supplier integrations, and remote access for technicians and OEMs. When any part fails (or is compromised), downtime, quality issues, and missed shipments compound fast.
That’s why IT services for manufacturing have evolved from “fix it when it breaks” support into proactive, production-aligned operations: designing resilient networks, securing IT/OT boundaries, standardizing devices across sites, and modernizing legacy apps without disrupting the line.
Today’s guide explains what a complete managed IT model includes, the benefits and risks, and how to select a partner and service levels that match real manufacturing constraints—shifts, safety, compliance, and continuous improvement.
Why IT Services For Manufacturing Matter In 2026
In 2026, “uptime” isn’t just an operations metric—it’s the output of tightly coupled IT, OT, suppliers, and security decisions. OT environments are more interconnected than ever because plants need efficiency, integration, and real-time visibility—but that same connectivity expands the attack surface and raises the consequences of failure.
IT/OT Convergence - Why The Factory Floor And Front Office Now Share Risk (And Responsibility)
IT and OT used to be treated like separate worlds. Today, they share identity systems, remote access pathways, shared networks, and data flows that support analytics and continuous improvement—so risks cross boundaries quickly. Modern OT guidance stresses that cybersecurity decisions must account for safety, reliability, and operational continuity—not just confidentiality.
A practical way to think about convergence is “control vs. observe.” Current OT connectivity guidance explicitly recommends ensuring monitoring/analytics/business systems do not have direct control capabilities over OT assets; they should be designed to observe and analyze, not command operations. This helps protect safety and reduces the blast radius of compromise.
Downtime Economics - How Small Outages Cascade Into Quality And Delivery Pain
A five-minute shop-floor outage is rarely “just five minutes.” It triggers scrap risk, rework, line rebalancing, missed changeover windows, rushed QA, and rescheduling across labor and logistics. That cascading effect is exactly why advanced manufacturing programs emphasize reducing downtime and improving overall equipment effectiveness—not as abstract KPIs, but as a direct productivity lever.
From a service design perspective, downtime economics changes how you prioritize fixes. A minor issue on a back-office device might wait; a flaky switch feeding a cell, a failed industrial workstation image, or a broken vendor access path becomes an incident that can stop revenue-generating operations. OT security guidance also highlights that cyber incidents can create physical harm or environmental impact, which raises the “cost of downtime” beyond dollars.
Security-Driven Urgency (What’s Changed Since 2024)
The threat trend line since 2024 has reinforced an uncomfortable truth: attackers don’t need exotic techniques when factories run a large, distributed footprint with varied patch levels, remote access tools, and third-party connections.
In the Verizon 2025 DBIR executive summary, ransomware is present in 44% of reviewed breaches (up from 32%), and exploitation of vulnerabilities is a growing initial access vector (reaching 20%). That matters for manufacturers because plants tend to have a long tail of edge devices, VPNs, and special-purpose endpoints that are harder to standardize.
The same report highlights supply chain and third-party exposure: breaches involving a third party doubled from 15% to 30%. In manufacturing environments, those “third parties” often include OEMs, integrators, and remote maintenance vendors—exactly the access paths OT guidance calls out as compounding risk.
The Critical Role Of Managed IT Services In The Manufacturing Industry
In manufacturing, managed IT isn't an “outsourced help desk.” It’s a delivery system for plant stability: standardized configurations, predictable support during shifts, measurable incident response, and security controls that don’t break production constraints. OT security guidance repeatedly emphasizes making risk-informed decisions, documenting them for auditability, and designing connectivity so compromise is harder and less impactful.
Managed vs. Break/Fix vs. Co-Managed - What Each Looks Like In A Plant Context
Break/fix is reactive: something fails, you open a ticket, someone shows up. That model tends to optimize for short-term ticket closure—not for preventing recurring outages, reducing configuration drift, or building recovery readiness.
Managed services are proactive and measured: monitoring, patch and configuration management, backup validation, security controls, and regular reporting against defined KPIs. These are the disciplines that turn “we think we’re stable” into “we can prove we’re stable.”
Co-managed is common in mature plants: your internal team retains ownership of plant applications, priorities, and governance, while a partner runs defined operational functions (monitoring, endpoint management, off-hours coverage, documentation, and escalation). This aligns well with OT guidance’s emphasis on clear accountability and auditable decisions.
Manufacturing IT vs OT
OT environments carry unique constraints: performance impacts, strict change windows, and the reality that safety, reliability, and uptime often outweigh “best practice” security defaults.
That’s why good manufacturing operating models define, in writing:
- Who owns what (IT owns identity? OT owns PLC network changes? shared decisions for remote access?).
- What approvals are required (especially for changes near control systems).
- How escalation works (24/7 routes, plant-on-call, vendor involvement, and safety sign-off).
For a structured way to map responsibilities, many teams align operational controls to the NIST Cybersecurity Framework 2.0 functions (Govern, Identify, Protect, Detect, Respond, Recover). It’s a practical vocabulary for cross-functional teams.
What “Production-Aligned SLAs” Actually Mean
A plant SLA is different from an office SLA because “severity” is defined by production impact. A true production-aligned model typically includes:
- Coverage that matches shift patterns and maintenance windows.
- A clear “stop-the-line” severity tier with fast triage and escalation.
- On-site response options and spare/replace strategies for critical endpoints.
Service desks are designed as a single point of contact and communication hub, which is especially important when multiple teams must coordinate during an incident (IT, OT, maintenance, and vendors).
Key Components Of Manufacturing IT Services In A Managed Model
A completely managed scope should be easy to visualize:
- What’s covered at the plant edge
- What’s covered in corporate systems
- What’s covered in the integration layer that connects them
That is the practical core of manufacturing IT services—and it’s how you compare providers without getting trapped in vague promises.
Manufacturing IT Services Checklist (Coverage Across Plant, Edge, Cloud & Corporate IT)
A useful checklist starts with outcomes and not tools. At minimum, you want defined accountability for:
- Asset inventory and configuration baselines
- Monitoring and alerting
- Identity and access controls
- Patch and vulnerability management (with OT-safe constraints)
- Backup and recovery testing
- Incident response procedures and reporting
If a provider can’t clearly describe what happens in the first 30–90 days—discovery, stabilization, and baseline reporting—that’s a red flag. OT guidance emphasizes documenting architecture and making risk-informed decisions auditable; your rollout plan should reflect that.
Network Management And Security For Plants, Warehouses, And Remote Sites
Plant networks must be designed so compromise is contained. Modern OT connectivity guidance recommends strong boundary controls that reside in a separate network segment—often called a DMZ—to isolate external-facing systems (like remote access gateways) from the core OT network.
Segmentation goes beyond “IT vs OT.” Guidance highlights zoning, micro-segmentation, and enforcing least-privilege traffic paths to reduce lateral movement and limit exposure—especially when legacy systems must remain in place.
Endpoint + Identity Management For Shared Workstations & Industrial PCs
Manufacturing endpoints behave differently:
- Shared workstations with shift handoffs
- Industrial PCs with specialized drivers and long replacement cycles
- “Shadow” endpoints owned by vendors or embedded into equipment
Security guidance for ransomware defense repeatedly emphasizes phishing-resistant MFA for key services, especially email and VPNs, alongside identity and access management controls. In plants, this often requires designing authentication and privilege models that don’t disrupt production roles (e.g., fast re-auth patterns, kiosk policies, segregated admin accounts).
Cloud/Hybrid Operations For ERP/MES Integrations & Standardized Tooling
Cloud isn’t the goal; stable integrations are. Industry 4.0 programs highlight how connected technologies (IoT, analytics, AI) can reduce downtime and improve quality—but only if data collection, storage, and transmission are designed securely and operationally.
The practical managed-services question is: who owns the integration reliability between plant systems and enterprise workflows, and how is it monitored? If you can’t detect broken interfaces quickly, you end up treating symptoms (late shipments, manual re-entry) rather than restoring the system behavior.
Backup, Disaster Recovery, And Recovery Testing For Production Continuity
Backup is not “set it and forget it.” The #StopRansomware guidance explicitly recommends maintaining offline, encrypted backups and regularly testing their availability and integrity—because ransomware actors often target accessible backups to make recovery impossible without paying.
In manufacturing, it’s not enough to back up files. You also need recoverable system states: golden images for critical servers, workstation images for production roles, and validated restore procedures aligned to the plant’s recovery priorities.
Help Desk + Field Support - How To Structure Triage For Manufacturing Severity Levels
A production-aware service desk does three things well:
- Captures context fast (site, line, safety impact, current shift constraints)
- Routes correctly (IT vs OT vs vendor vs facilities)
- Communicates clearly (operators don’t want “ticket updates”—they want time-to-recovery)
That’s why a well-run service desk is defined as the central point for incidents, service requests, and communication between teams—especially during high-severity events.
Challenges Faced By Manufacturing Companies
The biggest mistake manufacturers make is assuming the constraints they live with—legacy equipment, vendor access, multi-site variation—are “unique.” They’re common, predictable, and manageable, but only if your operations model acknowledges them explicitly.
Legacy Systems & Long Equipment Lifecycles - Why Patching Is Different In OT
OT environments frequently contain obsolete products due to extended lifecycles, and guidance warns that obsolete products may no longer receive security updates and may lack modern mitigations.
This changes patching behavior. You often need compensating controls—segmentation, hardened boundary controls, and tightly restricted access—while you plan realistic replacement timelines. OT cybersecurity guidance explicitly frames segmentation as a temporary measure alongside a roadmap for asset replacement.
Vendor & OEM Remote Access (The Hidden Attack Surface Most Teams Underestimate)
Remote access is a productivity enabler—but it’s also a common abuse path. #StopRansomware guidance notes the malicious use of remote access and remote monitoring/management software and recommends auditing tools and logs to detect abnormal use.
Modern OT connectivity guidance advises hardening the OT boundary with a DMZ that isolates external-facing systems such as remote access gateways and vendor portals from the core OT network. This architecture reduces the chance that a gateway compromise directly exposes OT assets.
Change Management On The Shop Floor: Training, Adoption & Operational Disruption Risks
Even “small” IT changes can disrupt production, like:
- Authentication prompts that slow operators
- Endpoint agents that affect performance
- Network rule changes that break machine-to-system communication
That’s why OT guidance calls for testing controls before deployment and for evaluating the operational impacts of security mechanisms, including latency and performance trade-offs.
Challenges in Integrating IT Support for Manufacturing
The integration challenge is organizational as much as technical. The 2025 DBIR highlights the growing role of third parties in breaches, reinforcing why plants must treat vendor access paths as governed, monitored, and auditable—not casual “log in whenever you need.”
A high-functioning model documents who can approve connectivity, which systems are in scope, and how isolation will work in an incident—because OT guidance treats these as “end states” you should design toward.
Managed IT Services For Manufacturing Companies
When buyers search for IT services for manufacturing, they’re usually trying to answer one question: “Can you keep operations stable while we modernize?” The best providers can describe coverage for the manufacturing stack, the site standardization approach, and a lifecycle plan that’s realistic for plant constraints.
Typical Manufacturing Stack Coverage - ERP, MES, SCADA, Historians, Data Pipelines
Manufacturing environments span enterprise planning down to shop-floor control. The International Society of Automation ISA-95 model describes layered levels from physical processes through sensing/control up to enterprise planning and logistics—useful context when defining what belongs in IT vs OT scope.
At the OT layer, NIST OT security guidance explicitly covers common OT components such as SCADA systems, PLCs, and DCS environments, and emphasizes that security controls must fit operational realities.
Multi-Site Standardization - How Managed Services Reduce Variability Across Plants
Variability is risk. Different switch configurations, inconsistent endpoint images, and “one-off” vendor remote access setups create fragility. OT connectivity guidance encourages centralizing and standardizing network connections to limit exposure and improve control.
Standardization also makes monitoring meaningful. If every plant reports incidents differently, your MTTR and uptime metrics become storytelling instead of management. The NIST CSF 2.0 emphasizes consistent outcomes and communication across stakeholders, which is exactly what multi-site reporting should enable.
Building A Lifecycle Plan: Asset Inventory, Refresh Cycles, And Supportability
A lifecycle plan starts with “what do we have?” and “what does it depend on?” That aligns with the Identify and Govern concepts in CSF 2.0, which exist to make risk management and prioritization explicit rather than informal.
For OT, you also need to identify what’s obsolete or unsupported and treat those items as higher-risk, then decide which compensating controls (segmentation, restricted access) apply until replacement.
Benefits Of Managed IT Services For Manufacturing Companies

The real ROI of IT services for manufacturing shows up in fewer “surprise” outages, faster recovery when incidents happen, safer modernization, and clearer accountability between IT, OT, and vendors. OT guidance frames resilience as raising the threshold needed to cause disruption—managed operations is how you do that consistently.
Uptime & Faster MTTR - Operational Continuity Outcomes Leadership Cares About
Leadership cares about outcomes: stable throughput, predictable delivery, and fewer escalations. A service desk model that’s designed to manage incidents and communication is foundational to reducing time-to-recovery—especially when multiple teams must coordinate.
Security reporting reinforces this need: ransomware appears in a large share of breaches, and vulnerability exploitation continues to rise as an entry path. Faster detection and response reduces downtime—even when prevention isn’t perfect.
Predictable Costs And Scalable Coverage Across Sites And Shifts
Predictable cost isn’t about cheaper IT—it’s about fewer cost spikes from emergency incidents, rushed replacements, and unplanned downtime. A managed model makes work visible: what is included, what is out of scope, and what a “major incident” costs.
Scalability matters because manufacturing is multi-site by nature. When practices are standardized (monitoring, patch cadence, access controls), new plants or lines can be onboarded to the same baseline rather than reinvented.
Stronger Cybersecurity Posture With Monitoring, Response & Recovery Readiness
The 2025 DBIR shows that third-party involvement in breaches doubled to 30%, reinforcing why monitoring, access governance, and incident readiness must include vendor ecosystems.
Ransomware defense guidance emphasizes MFA, least privilege, and backup testing—controls that only work when services are actually operated day-to-day (enrollment, audits, restore drills), not when they’re “planned.”
Compliance Readiness: Turning Service Reports Into Audit Evidence (Without Heavy Jargon)
Compliance is easier when reporting is disciplined. If you can show patch cadence exceptions, access reviews, backup test results, and incident timelines, audits often become verification rather than archaeology.
Many organizations build their security management systems around standards like International Organization for Standardization ISO/IEC 27001, which describes an information security management system approach. A managed services partner won’t “make you compliant,” but they can provide the operational evidence your governance program needs.
Productivity Gains For Engineering, Operations & Back Office Via Standardized Tools
Industry 4.0 programs emphasize that connected technologies can improve quality, shorten downtimes, and improve overall equipment effectiveness. Those gains depend on stable networks, reliable devices, and data pipelines that are supported like production systems—not like side projects.
Standardization also reduces “tribal knowledge” risk: fewer custom fixes, more repeatable onboarding, and clearer documentation for shift-to-shift continuity.
Managed IT Services for Manufacturing Use Cases
The best way to evaluate IT services for manufacturing is to map them to real plant scenarios. If a provider can’t explain how they handle segmentation, shared devices, vendor access, and recovery priorities, their playbook is probably office-first.
Plant Network Reliability & Segmentation
Segmentation is a reliability strategy as much as a security strategy. OT guidance recommends zoning, separation of duties, and boundary controls (like DMZs) to prevent a compromise or misconfiguration from becoming a plant-wide event.
For a widely used reference model, the Purdue architecture is often used to reason about separating industrial control networks from corporate networks and the internet. A U.S. Department of Energy topic paper describes it as a framework for segmentation and notes its use as a baseline for OT security approaches.
End-User Support For Production Roles
Production support is about speed and clarity. Shared workstations and constrained environments need fast user restoration patterns and clear escalation to OT or vendors when symptoms point outside typical IT scope.
This is where a mature service desk matters: it’s the communication hub that logs, prioritizes, and coordinates incident resolution, which reduces confusion during multi-team incidents.
Predictive Maintenance Enablement
Predictive maintenance only works when the boring layers work first: reliable connectivity, consistent data capture, secure remote monitoring, and clear ownership of data pipelines. OT guidance explicitly lists benefits like predictive maintenance and remote monitoring as drivers of connectivity—while warning these introduce risks.
Industry 4.0 guidance similarly points to IoT, analytics, and AI as enablers of efficiency and reduced downtime, but it also emphasizes that cybersecurity can’t be ignored as interconnectivity rises.
Supply Chain Visibility & Integration Reliability
Supply chain visibility is often an integration story: EDI/API flows, portals, supplier status feeds, and shared scheduling data. When those connections are unstable, people revert to spreadsheets and phone calls—slowing response times and increasing error rates.
Third-party risk trends—like DBIR’s rise in third-party involvement—underscore why these integrations should include access governance and monitoring rather than “set it up once.”
Quality Control And Traceability (Data Integrity + Retention + Access Controls)
Traceability depends on data integrity: accurate timestamps, controlled access, and retention policies that match regulatory or customer requirements. Controls like identity management and access control are explicitly part of the Protect function in CSF 2.0.
For OT-adjacent systems, you also need to ensure security controls don’t degrade operational performance or create unsafe behavior—an explicit trade-off OT security guidance addresses.
Business Continuity And Disaster Recovery
Ransomware guidance is clear: keep offline encrypted backups and test them. OT-aware recovery adds another layer: restore order matters (identity, remote access gateways, production apps, then “nice to have”), and isolation plans must be defined so you don’t re-infect clean systems during recovery.
Real World Examples Of How Managed IT Services Help Manufacturers
The scenarios below are composite examples based on common manufacturing failure modes and the control patterns recommended in modern OT and ransomware guidance.
Example 1: Reducing recurring downtime via monitoring + root-cause fixes (not just ticket closure)
A plant experiences recurring micro-outages every week—short, inconsistent, and hard to diagnose. A managed team implements baseline monitoring, correlates incidents to network events, and identifies a misconfigured boundary rule that intermittently drops a critical path. A permanent fix is validated during a planned window, and the pattern disappears.
The key difference is operational discipline: detect, analyze, fix root-cause, and standardize—rather than repeatedly closing similar tickets. That approach aligns with CSF’s Detect/Respond outcomes and the broader push toward measurable resilience.
Example 2: Securing vendor remote access without blocking maintenance windows
A manufacturer relies on multiple OEMs for urgent remote diagnostics. Instead of allowing direct VPN access into the plant network, the environment is redesigned so remote access terminates in a DMZ buffer zone, with controlled pathways into OT networks and comprehensive logging.
This reflects current OT connectivity principles: harden the OT boundary, limit exposure, and ensure all connectivity is logged and monitored to make compromise detection easier.
Example 3: Standardizing multi-plant IT operations (shared baselines, shared reporting)
A multi-site manufacturer grows by acquisition and inherits unique setups in each location. A managed model establishes standard endpoint images, identity policies, backup validation routines, and a uniform incident taxonomy so leadership gets comparable KPIs across all sites.
The security payoff follows the operations payoff: consistent controls reduce unknown gaps—an organizational factor ransomware research suggests contributes to incidents.
Steps To Successfully Implement & Integrate Managed IT Services In Manufacturing

A good rollout plan prioritizes stability and safety first, then security hardening, then standardization and continuous improvement. OT guidance repeatedly emphasizes auditable decisions, boundary hardening, logging, and isolation planning—so implementation should mirror those priorities.
Step 1: Discovery And Baseline (Asset Inventory, Dependency Mapping, Risk Snapshot)
Start by building a clear system map: critical assets, network paths, integrations, and key vendor access routes. If you can’t diagram it, you can’t defend it—especially when guidance emphasizes documenting architecture and making decisions auditable.
This is also where you establish current KPIs: incident frequency, top recurring issues, current restore times, and known end-of-life assets.
Step 2: Stabilize First (Monitoring, Backups, Identity, Top Recurring Incidents)
Stabilization is the foundation: monitoring coverage, backup validation, and identity hygiene. Ransomware guidance stresses offline encrypted backups with regular testing and strong MFA practices—these are “first 30–60 days” controls, not year-two improvements.
In OT-adjacent environments, ensure monitoring agents and scanning approaches are tested so they don’t degrade device performance or disrupt production systems.
Step 3: Secure the IT/OT Boundary (Segmentation, Remote Access, Logging)
This is where IT services for manufacturing become unmistakably different from office IT. You implement boundary controls (DMZ), restrict paths, and enforce least-privilege connectivity so a compromise doesn’t become a safety or uptime incident.
You also formalize logging and monitoring rules because OT guidance treats monitoring as the “last line of defense” and explicitly links logs to anomaly detection and faster compromise identification.
Step 4: Standardize Across Plants (Tooling, Patch Cadence, Documentation)
Standardization reduces variability risk. OT connectivity principles recommend centralizing and standardizing connections, while CSF 2.0 emphasizes structured outcomes and consistent risk management.
Documentation is not bureaucracy—it’s operational memory. Build runbooks for common incidents, vendor procedures, and recovery sequences, and keep them accessible during outages.
Step 5: Continuous Improvement (Monthly Ops Review + Quarterly Security Review)
Sustained results come from routine governance: monthly operational reviews, quarterly security reviews, and periodic recovery exercises. This maps directly to CSF’s Govern and Recover concepts and to ransomware guidance emphasizing testing and lessons learned.
A simple cadence is often enough: update the risk register, review major incident trends, verify backup test results, and track standardization progress.
Challenges Of Managed IT Services In The Manufacturing Industry

Managed services can fail in manufacturing when governance is unclear, tooling becomes a black box, or the provider applies a generic MSP playbook that ignores OT constraints. The solution isn’t avoiding managed services—it’s designing the engagement to fit plant reality.
Loss Of Control Concerns - Governance Models That Keep Accountability Internal
If your leadership worries about “losing control,” define what cannot be outsourced: production priorities, safety sign-off, OT change approvals, and final decision rights for connectivity. CSF 2.0’s Govern function is a useful lens here: the business must own risk expectations and oversight.
The provider’s job is to execute within that governance: measurable operations, transparent reporting, and agreed escalation paths.
Service Gaps - How To Spot “Generic MSP Playbook” Risk Early
If a provider can’t explain how they handle DMZ design, OT boundary hardening, or performance-safe monitoring, they may not be ready for plant environments. OT guidance is explicit on boundary controls and the need to consider operational constraints.
A second warning sign is vague security posture claims without evidence. You want routine backup test proof, MFA enforcement reporting, and logged/monitored connectivity—because those are repeatedly recommended in ransomware and OT guidance.
Onboarding Friction - Plan For Brief Interruptions And Access Transitions
Onboarding always causes some turbulence: privilege handovers, tooling deployment, documentation gaps, and changes to how people request support. The right move is to plan onboarding around production windows and to test controls in non-critical areas first to avoid disruption.
Clear communication reduces resistance: what changes, why it changes, and how escalation works during a major incident.
Tooling Transparency & Exit Planning (Prevent Lock-In From Day One)
Lock-in is usually a documentation and access problem, not a technology problem. Require:
- Named admin access policies (who owns credentials, rotation, break-glass)
- Exportable logs and reports
- Runbooks and diagrams stored in your systems
- Clear separation of duties so vendors can’t become single points of failure
This also aligns with OT guidance that emphasizes auditable reasoning and centrally stored documentation for connectivity decisions.
8 Critical Requirements Of Managed IT Services For Manufacturing Companies
If you’re evaluating IT services for manufacturing companies, focus on requirements that predict success under real plant constraints: safety, uptime, vendor access, and operability across sites. Use this as a scorecard for RFPs and shortlist decisions.
1. Understanding of Industrial Controllers
You don’t need a provider to program controllers, but they must understand operational sensitivity: why certain endpoints cannot be scanned aggressively, why patching is constrained, and why changes must align to maintenance windows.
Look for evidence they understand performance trade-offs and the safety implications of cyber incidents, which OT security guidance treats as core risk factors.
2. Knowing CAD/CAM and PLM-Adjacent Workflows
Engineering toolchains can be storage- and network-intensive, and performance issues can quietly become production issues (delayed revisions, wrong versions, missed changeovers). A strong provider treats these workflows as critical services, not “power user” exceptions.
The practical question: can they monitor performance end-to-end and prove improvements over time?
3. Comprehending Shop-Floor Realities
Plant support is a human system. Providers must show how they handle shift handoffs, shared devices, and high-severity incidents during nights/weekends. The service desk’s communication role becomes central here.
They should also demonstrate a safety-aware mindset—because OT cybersecurity decisions must account for potential human and environmental impacts.
4. ERP and MES Competence
ERP/MES stability is often the hidden limiter on throughput and traceability. A qualified partner can describe how they monitor interface health, manage access controls, and prioritize recovery sequences in disruptive events.
Ask how they prevent “fixes” that unintentionally break integrations across plants or suppliers.
5. Great Skills At Hardening Your Network
This is table stakes. Modern OT connectivity guidance is explicit about boundary controls (DMZ), segmentation, and comprehensive logging and monitoring to make compromise detection easier.
Also validate they can support segmentation without disrupting operations—micro-segmentation and protocol-aware controls are powerful, but they require careful design.
6. Modernization Roadmap
The best partners don’t just operate systems; they bring a modernization roadmap grounded in measurable outcomes: reduced recurring incidents, improved recovery times, reduced downtime drivers, and safer connectivity patterns.
A roadmap should be realistic about legacy timelines and should treat segmentation as part of a broader lifecycle plan—not as a permanent substitute for modernization.
7. Proven Incident Response + Recovery Testing Capability
Ransomware guidance emphasizes tested backups, isolation, and recovery discipline. A partner should be able to show how often recovery tests run, how results are documented, and how lessons learned feed into improvements.
Also ask how they handle vendor access during incidents—because you may need to shut down connectivity to contain spread while still preserving a path for safe recovery actions.
8. Reporting Discipline
Reporting is where managed services either create trust or erode it. Require clear KPIs (uptime, MTTR, backup test pass rate, patch cadence exceptions, access review cadence) and plain-language executive summaries.
This also supports governance expectations in CSF 2.0, where oversight and communication are part of making cybersecurity a managed business risk.
IT Services Manufacturing: Operating Models, SLAs & Pricing
When you evaluate IT services manufacturing, you’re not buying tools—you’re buying an operating model. The simplest way to avoid disappointment is to define what “done” means in SLAs, how escalations work during production, and which metrics will be reported monthly.
IT Services Manufacturing Pricing Models
Different service models fit different manufacturing environments, so the right choice depends on your plant footprint, support scope, and uptime requirements.
Common pricing models include:
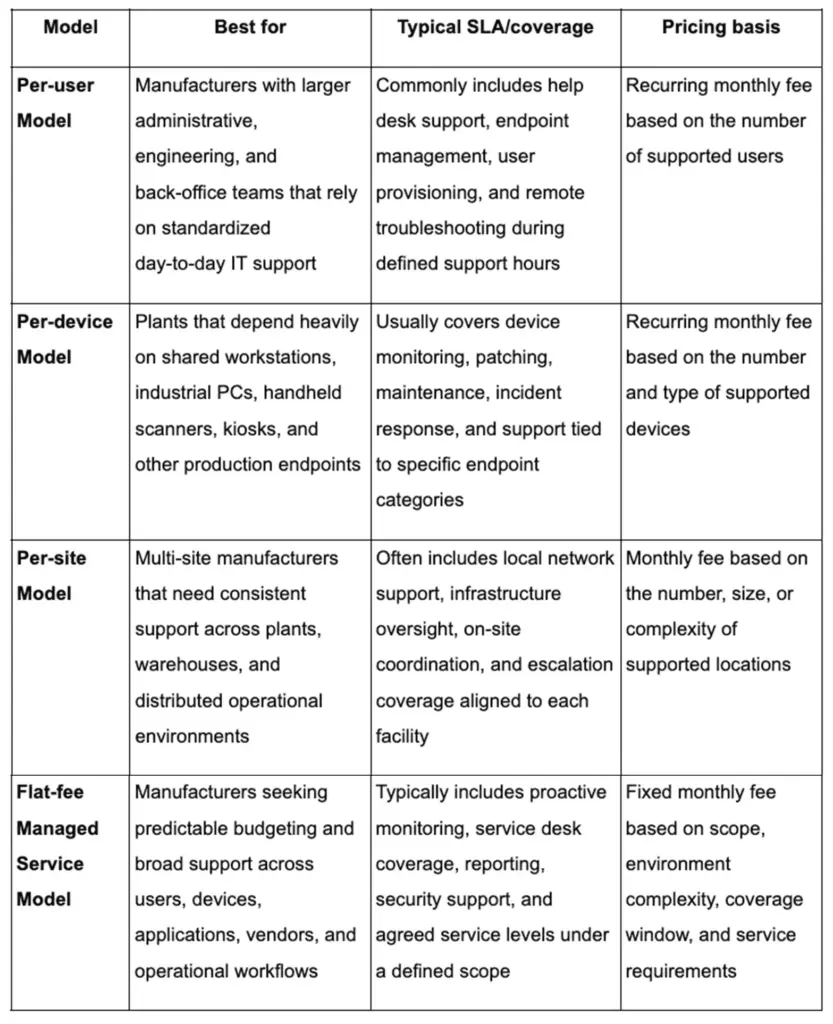
The key is mapping pricing units to manufacturing reality: include industrial PCs, shared workstations, network gear coverage expectations, and onsite response assumptions.
Service Levels That Match Manufacturing Reality
Manufacturing service levels often require:
- 24/7 or near-24/7 coverage aligned to shifts
- Defined major incident process
- On-site dispatch options for critical failures
- Vendor coordination playbooks for specialized equipment
If you have multiple sites, require clarity on who is “first responder” vs “escalation” and how cross-site incidents are managed.
KPI Requirements In Contracts
A practical KPI set should include:
- Incident response time by severity
- MTTR for production-impact incidents
- Patch cadence and exceptions list (with OT-safe rationale)
- Backup test frequency and pass rate
- RPO/RTO targets aligned to production priorities
This aligns with CSF’s emphasis on readiness across Respond/Recover tracks—not just “security controls exist.”
How To Avoid Lock-In
To prevent lock-in, you require:
- Documentation stored in your repository
- Admin access and credential governance defined contractually
- Exportable reports/logs
- Clear separation of duties and boundary control principles
OT connectivity guidance reinforces the value of standardized, centrally stored decisions and documentation; that mindset should apply to vendor relationships too.
Trends Shaping The Role Of IT Services In Smart Manufacturing
Plants are becoming software-defined environments—driven by sensors, connected systems, analytics, and increased automation. Industry 4.0 guidance explicitly frames this shift as automation using technologies like IoT, big data analytics, and AI, with benefits that include shorter downtimes and improved quality.
Edge Computing And Real-Time Analytics
Edge computing is best understood as moving computers closer to data sources to improve responsiveness and bandwidth efficiency. IBM describes edge computing as bringing enterprise applications closer to data sources such as IoT devices or local edge servers, enabling faster insights and improved response times.
In manufacturing, edge helps when latency and connectivity constraints are real (workcells, vision, near-real-time alarms). It’s noise when it becomes a branding exercise without clear ownership, monitoring, and recovery plans.
AI-Assisted Monitoring & Maintenance (Realistic Operational Use Cases)

Security reporting in 2026 increasingly highlights AI-accelerated attacks and a rise in exploitation of public-facing systems—pressuring defenders to use automation and analytics efficiently.
In operations, the “real” AI wins are often narrow: anomaly detection that reduces false positives, predictive flags that improve maintenance planning, and analytics that make root-cause work faster. Industry programs emphasize that data analytics and AI can support smarter decisions, but only when data collection and monitoring are reliable.
Security Frameworks Becoming Operational Requirements
Standards and frameworks are becoming operational requirements because audits, customers, and insurers increasingly ask for demonstrable security practices. The ISA/IEC 62443 framework is explicitly lifecycle-oriented and designed for industrial automation and control systems, including zones/conduits and service provider responsibilities.
At the enterprise level, CSF 2.0’s Govern/Identify structure helps align plant security decisions to business risk and supply chain relationships—valuable when third-party involvement in breaches is rising.
Resilience-First Architecture - Recovery Testing & Segmentation Becoming “Table Stakes”
Resilience is increasingly defined by two operational truths:
- Assume incidents will happen (including ransomware and vendor compromise paths).
- Design networks so incidents are contained and recovery is practiced.
That’s why offline backup testing and boundary/segmentation controls are moving from “nice to have” to “expected.” OT guidance reinforces DMZ boundary patterns and monitoring as core defenses, while ransomware guidance emphasizes tested, offline backups.
How BrainX Comes Into The Picture
BrainX fits best when manufacturers need more than an MSP. For organizations aligning IT services for manufacturing with modernization goals, BrainX supports custom application modernization, ERP/MES integration stability, DevOps-led reliability, and long-term support without disrupting operations.
Engagements can range from project delivery with a controlled cutover plan to ongoing maintenance and operational support.
For a productive first call, bring your system map, downtime history, security constraints, and success metrics.
BrainX even follows an ISO 27001-aligned information security approach, which matters when manufacturing environments involve sensitive IP, regulated data, or complex access requirements.
To learn more, see our case studies and service pages (e.g. our DevOps services and software maintenance and support), which show how we’ve helped other manufacturers bridge IT and OT with minimal disruption
FAQs
What do IT services for manufacturing typically include?
A well-scoped package usually includes network operations, endpoint and identity management, monitoring, incident response workflows, backup and recovery testing, and governance around remote access and third-party connectivity. OT guidance emphasizes boundary controls, logging/monitoring, and risk-informed connectivity decisions, while ransomware guidance emphasizes offline backup testing and MFA.
How are managed IT services for manufacturing different from standard office IT?
Manufacturing managed services must work under safety and uptime constraints, where some security actions can’t be deployed “like IT” without testing performance impacts. OT security guidance discusses the need to consider latency, reliability, and safety trade-offs when implementing controls, and OT connectivity guidance emphasizes boundary hardening and segmentation to reduce operational disruption risk.
What does co-managed IT look like for manufacturing plants?
Co-managed IT usually means your internal team retains governance, production priorities, and OT change approvals, while a partner runs defined operations (monitoring, help desk, patching processes, documentation, reporting, and off-hours coverage). Using CSF 2.0 language, your organization retains Govern accountability while the partner executes parts of Identify/Protect/Detect/Respond/Recover.
How much do managed IT services cost for manufacturers?
Pricing varies based on coverage hours, number of sites, endpoint types (including industrial PCs), on-site response needs, and security scope (remote access governance, logging, recovery testing). For reliable expectations, require a clear service catalog and SLA metrics that reflect plant operations, plus evidence-based security and recovery practices (like tested offline backups).
What should we demand in an SLA for multi-shift production?
At minimum: severity definitions based on production impact, 24/7 escalation paths aligned to shifts, response/restore targets, backup test cadence, and clear ownership of vendor coordination and OT boundary controls. OT connectivity guidance stresses boundary hardening and monitored connectivity, and CSF 2.0 emphasizes readiness across Respond/Recover.
A complete approach to IT services for manufacturing should make plant reliability predictable: standardize what can be standardized, secure what must be connected, and practice recovery so incidents become manageable events—not existential outages.