TL;DR / Key Takeaways
- A backend app development company should scope more than “server code” such as APIs, data modeling, auth, infrastructure, CI/CD, observability, and reliability.
- Request proposal deliverables for things such as OpenAPI/Swagger specs, database schema/migration, CI/CD pipelines, monitoring dashboards and runbooks.
- Stack decisions should be made based on constraints: traffic pattern, data consistency requirements, compliance, and capability of your team that will be operating the system.
- The costs vary greatly based on the specific drivers behind your particular backend, such as RBAC/SSO, third party integrations, real-time features, and availability targets.
- Prioritize using a vendor evaluation scorecard: security practices, DevOps maturity, testing strategy, measurable system performance and clarity of estimates.
If your app slows down under load, ships bugs too often, or becomes risky to change, the backend is usually where the real problems live. This guide is designed to help you evaluate a backend app development company like a buyer—not just a reader—so you can scope correctly, understand what “backend” actually includes, and budget with fewer surprises.
You’ll learn what deliverables to demand in proposals, which tech stack choices matter (and which are just preferences), and how vendors typically estimate backend work for MVPs through enterprise-grade systems.
What Is Backend Development? A Clear Breakdown
Backend development involves creating the hidden parts of an application, such as handling data storage and retrieval, business rules, authentication, and returning responses via APIs. It's what will make your app fast, secure, and reliable as users increase.
A practical way to think about the backend is “everything required to deliver trusted outcomes to the client”—web app, mobile app, partner systems, or internal tools. If the frontend is the interface, the backend is the engine, transmission, and safety system.
Modern backend work also includes operational responsibilities. The fast delivery of shipping features is just one part of the equation; the other part is to be able to deploy the shipping feature fast, monitor it constantly, and recover quickly when things go wrong.
Finally, backend development is not “one technology.” It’s a set of decisions across APIs, data, architecture, hosting, security, and DevOps—and those decisions compound over time.
A Brief History of Backend Development
What we now call backend development grew out of earlier client-server and multi-tier application models. As software moved from centralized systems to distributed applications, more logic shifted to servers so clients could stay lighter while shared services handled data, business rules, and integrations. Over time, web servers, CGI scripts, application servers, and later API-driven architectures turned that server-side layer into the backend discipline teams rely on today.
In practical terms, the backend evolved from “the part that stores and processes data” into a broader operational layer that also covers authentication, integration, deployment, and reliability. That is why modern backend discussions are no longer just about databases or server code. They are about how the system behaves in production and how safely it can scale over time.
Key Backend Features and Components
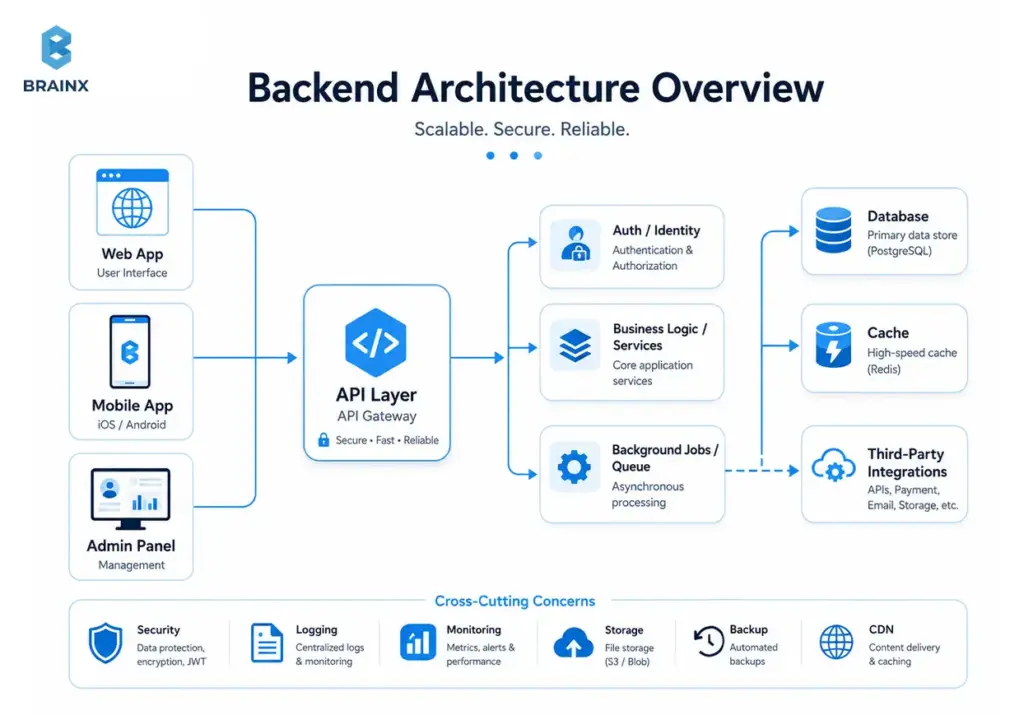
A backend is not just a server running code. It is a collection of connected components that handle requests, process logic, manage data, enforce security, and keep the application stable in production. Understanding these core parts helps buyers evaluate scope more accurately before comparing vendors or estimates.
The most common backend components include the API layer, business logic layer, database layer, authentication and authorization controls, background job processing, and infrastructure services such as hosting, caching, monitoring, and deployment automation. In modern products, observability is also a core component because logs, metrics, and traces are what allow teams to operate the system safely after launch.
In practical terms, each component serves a different purpose. APIs expose functionality to web and mobile clients. Services handle workflows and business rules. Databases store and retrieve application data. Auth systems control identity and permissions. Queues and workers handle asynchronous tasks. Infrastructure and DevOps practices keep releases safe, repeatable, and measurable. Together, these components determine whether a backend is only functional or truly production-ready.
Benefits of Strong Backend Development
A strong backend does more than make an application work. It gives the product stability, security, and room to grow without forcing the team into constant rework. When the backend is designed well, it becomes easier to ship features with confidence, support more users, and keep performance predictable as the product evolves.
One of the biggest benefits is reliability. Clean backend architecture reduces the risk of brittle APIs, unsafe deployments, and inconsistent data handling. That means fewer production surprises, faster debugging, and a smoother experience for users. It also improves product velocity because teams can add features without breaking unrelated workflows or fighting hidden technical debt.
Strong backend development also creates business value. It improves security posture, supports integrations more cleanly, makes compliance easier to approach, and gives decision-makers a more realistic path to scale.
In practical terms, a better backend usually means lower long-term maintenance cost, more predictable delivery, and a product that can keep growing without becoming fragile.
Definition and Role of Backend in Software Systems
The backend is the system of services that receives requests, validates, performs business logic, reads/writes data and returns responses, typically via HTTP APIs or event streams. It also regulates access, auditability and consistency and that is why often the quality of the backend tracks directly with customer trust.
In most products, the backend is responsible for:
- Business rules (pricing, permissions, workflows, validation)
- Data lifecycle (create/read/update/delete, history, retention)
- Security controls (authentication, authorization, secrets handling)
- Integrations (payments, email/SMS, identity providers, analytics)
- Reliability (retry logic, idempotency, graceful degradation)
It also shapes the speed of product iteration. Every new feature will take longer, be more costly, and become more difficult if your backend is hard to change, and that may be due to the brittleness of APIs, the risk of migrations, manual deployments, or all three.
A clean backend design creates leverage: stable contracts, predictable performance, and an architecture that can evolve without rewriting everything.
What a Backend App Development Company Does (and What “Backend” Includes)
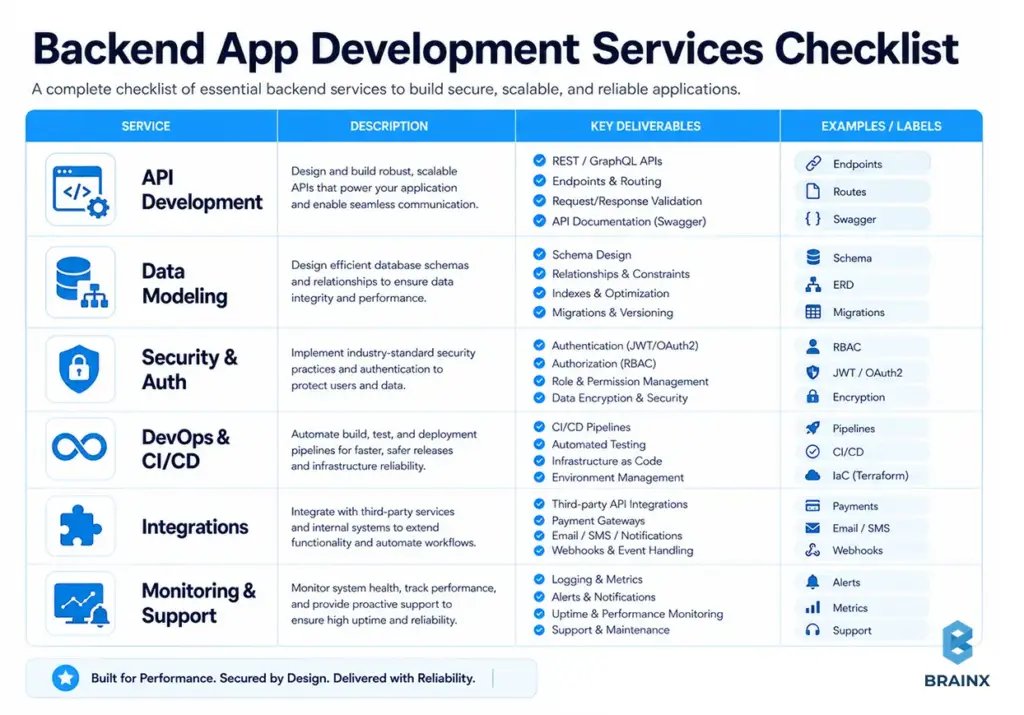
A reliable backend app development company should scope backend work beyond writing endpoints. In practice, backend delivery includes APIs, data design, security, cloud infrastructure, automated delivery pipelines, and the operational guardrails needed for production.
In real projects, here are some of the elements that are found in the “backend” part:
- API layer: REST/GraphQL endpoints, validation, pagination, versioning, idempotency
- Service layer: business logic, workflows, background jobs, queues, schedulers
- Data layer: schemas, migrations, indexing, caching, search, analytics pipelines
- Auth & security: JWT/OAuth, RBAC, SSO, secrets management, encryption
- Infrastructure: environments, networking, managed services, IaC
- Delivery: CI/CD, testing strategy, code quality gates, release management
- Observability: logs/metrics/traces, dashboards, alerting, runbooks, on-call readiness
When looking into the vendors for app backend development, make sure they clarify where each of these responsibilities falls – in their team, your team, or both – and what's covered when you add their services to the invoice.
Key Responsibilities of Back-End Developers
Back-end developers are responsible for turning product requirements into secure, reliable, and maintainable system behavior. Their job is not limited to writing server-side code. In practice, they design APIs, implement business logic, model and manage data, enforce authentication and authorization, and make sure the application can operate safely in production.
A major part of their responsibility is building stable foundations for growth. That includes defining clean service boundaries, handling database changes safely, integrating third-party systems, and making sure requests, workflows, and background jobs behave predictably under real usage. They also work closely with frontend teams so UI flows, API contracts, and edge cases stay aligned throughout delivery.
Modern backend responsibility also includes operational thinking. Strong back-end developers care about deployment safety, observability, rollback readiness, and incident prevention, not just feature completion. In other words, they are responsible for building a backend that is not only functional on launch day, but also resilient enough to support future releases, scaling, and long-term maintenance.
Common Backend Development Use Cases
Backend development becomes especially important when an app needs more than a basic interface. The clearest use cases include products that rely on secure user accounts, role-based permissions, third-party integrations, real-time activity, complex business rules, or large volumes of structured data. In these cases, the backend is what turns product requirements into reliable system behavior.
Common examples include SaaS platforms with multi-user workflows, marketplaces with payments and order logic, mobile apps with authentication and sync, internal tools that connect to CRMs or ERPs, and customer-facing platforms that need dashboards, notifications, and audit trails. Even when the frontend looks simple, the backend may still carry most of the complexity if the product has to coordinate data, permissions, events, and external services.
This is also where a backend app development company becomes more valuable than a general coding vendor. Once the product requires uptime targets, clean API contracts, migration planning, observability, and secure integrations, the backend stops being just a technical layer and starts becoming a business-critical system.
Also Read: Fintech App Development Cost Guide With Detailed Breakdown
Industry Adaptation in Backend App Development
Backend requirements are rarely identical across industries. Two apps may look similar on the surface, but the backend expectations can be very different depending on the type of data involved, the level of compliance required, and how critical uptime is to the business. That is why a strong backend partner should adapt architecture decisions to the operating reality of the industry, not just the feature list.
For example, healthcare and fintech products often need stricter access control, audit logs, data retention rules, and stronger safeguards around sensitive information. Ecommerce and marketplace platforms usually put more pressure on integrations, inventory sync, order workflows, payment reliability, and traffic spikes during campaigns or seasonal demand. B2B SaaS platforms often need tenant isolation, role-based permissions, admin controls, reporting, and SSO support for enterprise customers.
This matters during scoping because industry context changes both effort and risk. A backend that works for a basic internal tool may be completely insufficient for a regulated platform or a customer-facing SaaS product. The best vendors do not treat backend architecture as generic. They shape it around the operational, compliance, and growth pressures of the business the product is meant to serve.
App Backend Development vs Full-Stack Development
The decision between backend-only and full stack depends on coordinating costs and ownership clarity. If you already have a good UI team, you can hire only the back-end personnel, but with well-defined API contracts and QA duties.
One vendor can minimize handoffs if you require frontend and backend app development. A single team can design the API with the UI flows in mind, align error handling, and run integrated testing earlier.
When splitting vendors, make sure you define:
- API ownership (who writes and versions specs)
- Contract testing strategy (who ensures compatibility)
- Release sequencing (backend-first vs UI-first)
- Shared definitions (error formats, pagination, auth flows)
A common failure mode is “backend finished” meaning “endpoints exist,” while the frontend team can’t ship because edge cases, permissions, and performance weren’t validated against real UI flows.
Typical Backend Deliverables You Should Expect in a Proposal
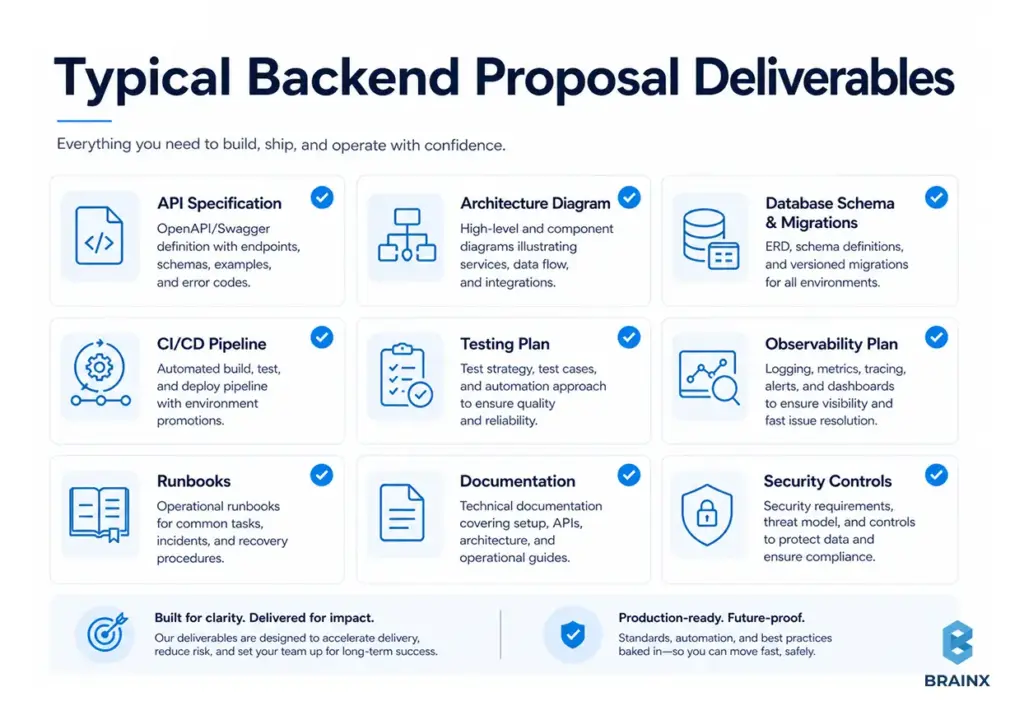
Proposals should list concrete artifacts and not just say, “we’ll build the backend.” The deliverables below are practical signals of maturity and reduce ambiguity later.
A proposal should usually contain the following:
- API specification (OpenAPI/Swagger or GraphQL schema), including error models
- Architecture diagram (services, data stores, integrations, trust boundaries)
- Database schema + migration plan, plus seed/test data strategy
- Outline of the CI/CD pipeline (build, test, security scans, deploy, rollback)
- Testing plan: unit, integration, contract, performance, security testing scope
- Observability plan: dashboards, alerts, log structure, tracing approach
- Runbooks: incident response basics, operational SOPs
- Documentation: setup, deployment steps, environment variables, secrets handling
If these are missing, you’ll often pay later—either through rework or operational instability.
Backend App Development Services You Can Outsource (Scope Checklist)
Most buyers underestimate how wide the backend scope can be. Generally, backend app development services cover the entire range of product engineering and production readiness, and can vary depending on the stage you are at, may it be developing an MVP, growing after the product-market fit, or modernizing an enterprise platform.
Ideally, outsourcing is a concept that will allow you to frame the scope in terms of outcomes (latency, uptime, compliance readiness) and artifacts (API specs, monitoring) instead of just tickets. The framing also improves estimation accuracy.
Use the checklist below to map what you need now vs later. A strong vendor will help you phase this work instead of pushing everything into v1.
API Development (REST/GraphQL), Versioning, and Documentation
A “good API” is not merely functional, it is consistent, predictable and safe for evolution. Ask your vendor how they implement resource naming, pagination, filtering, error responses, idempotency keys and backward compatibility changes.
What to request explicitly:
- OpenAPI/Swagger for REST endpoints (or a GraphQL schema + conventions)
- Versioning policy (URI versioning vs header-based vs evolutionary design)
- Contract testing or schema validation in CI
- Clear auth requirements per endpoint (scopes/roles)
- Rate-limiting and abuse controls where relevant
If your system has multiple clients (web, iOS, Android, partners), API consistency becomes a multiplier for delivery speed.
Database Design, Data Modeling, and Performance
Database choices and schema decisions are among the most expensive to change later. A competent team will start with your data access patterns, not just your entities.
Core backend data work includes:
- Relational vs NoSQL decisioning (consistency vs flexibility vs throughput)
- Normalization trade-offs (read-heavy vs write-heavy)
- Indexing strategy and query plans
- Migration tooling and rollback safety
- Caching strategy (what, where, TTLs, invalidation)
The most common causes of performance issues arise when patterns are mismatched, such as attempting to write an OLTP system with read models, or writing chat-like real-time workloads without considering concurrency.
Authentication, Authorization (RBAC), and Security Hardening
Security is not a feature you “add at the end.” Backends enforce identity and permissions, protect sensitive data, and prevent abuse.
Expect support for:
- OAuth 2.0 / OpenID Connect flows where appropriate
- JWT session handling and refresh strategies
- RBAC (roles) or ABAC (attributes), depending on complexity
- MFA and SSO integration for B2B products
- Secrets management (no secrets in code or CI logs)
- Encryption in transit + at rest, and key management practices
Question if they adhere to the OWASP guidelines and what they do with secure defaults (CORS policies, input validation, rate limiting, dependency scanning).
Cloud Infrastructure, DevOps, CI/CD, and Observability
A backend that can’t be deployed safely will slow your team down. Infrastructure and delivery automation should be part of the build, and should not be treated as a “later” project.
Here’re some key capabilities to look for:
- Infrastructure as Code (IaC) (Terraform, Pulumi, CloudFormation)
- CI/CD pipelines with quality gates (tests, linting, SAST)
- Environment strategy (dev/stage/prod parity)
- Observability (structured logs, metrics, tracing, dashboards, alerts)
- Rollback strategy and release methods (blue/green, canary, feature flags)
If a vendor claims, “We do DevOps.” Don’t just take their word for it. Ask for examples: what tools, what alerts, what runbooks, and how they handle incident response.
Integrations (Payments, Maps, CRM/ERP, Messaging)
One of the most significant complexity multipliers in the backend is integrations. They bring external constraints like rate limits, webhook retry semantics, idempotency requirements, and changing third-party APIs.
Common integration types:
- Payments (Stripe/Adyen), subscriptions, invoicing, tax
- Email/SMS/push notifications
- Maps/geocoding and routing
- CRM/ERP (Salesforce, SAP, NetSuite) and data sync
- Identity providers (Okta, Azure AD), SCIM provisioning
Request clear design when it comes to webhooks (verification, retries, deduplication) and integration testing in CI.
Maintenance, Monitoring, and SRE-style Support (Post-Launch)
Launching is the start of operational reality: incidents, performance regressions, dependency vulnerabilities, and evolving requirements. Your vendor should provide you with a transparent support model.
A mature post-launch offering includes:
- SLAs/SLOs (even if lightweight at first)
- On-call or defined escalation paths
- Regular patching and dependency updates
- Monitoring and alert tuning
- Backlog triage and technical debt budgeting
- Incident postmortems and preventive actions
If your app is revenue-critical, ask how they handle “P1 at 2 a.m.” and what’s included vs billed separately.
Common Backend Tech Stacks (and How to Choose the Right One)
A reliable vendor won’t push a trendy stack by default. The technologies, a backend app development company suggests, should depend on the following limitations: time to market, hiring limitations, compliance requirements, performance goals, and operational maturity.
The best stack is likely the one that your team can comfortably operate. For startups, it could be the case of settling for boring but well established tools with good ecosystems and predictable pricing. For enterprises, it could be about aligning with internal standards, governance, or even pre-existing cloud engagements.
Use the comparison mindset below: choose frameworks that reduce risk in your context, not in the abstract. Also consider the “second order effects”: deployment complexity, observability tooling, and developer onboarding.
Languages & Frameworks (Node.js, Python, Java, .NET, Go)
Each ecosystem can build great backends. The trade-offs show up in performance characteristics, tooling, hiring pools, and library maturity.
- Node.js (NestJS/Express/Fastify)
Ideal for API-rich products, real-time applications and teams already using TypeScript. Be aware of CPU intensive workloads and ensure that async patterns are consistent. - Python (Django/FastAPI)
Great for rapid development and AI related workloads. FastAPI offers strong performance for APIs with typed schemas. Ensure you plan for concurrency and background jobs properly. - Java (Spring Boot)
Strong enterprise fit for its advanced tooling, observability and performance tuning. Good choice when the system is complex, compliance heavy, and long-term. - .NET (ASP.NET Core)
High performance, great tooling, strong enterprise adoption, and good fit with Azure ecosystems. Often a strong choice for B2B SaaS platforms. - Go
Ideal for services that are performance-driven. Easier to use for concurrent models and light usage. The ecosystem is solid but you'll want experienced engineers to ensure designs are kept clean.
Understand the vendor decisions based on your requirements: latency, throughput, audit requirement, and team's expertise.
Databases (PostgreSQL/MySQL, MongoDB, Redis, Elasticsearch)
Most products work best with a transactional database beneath them like PostgreSQL or MySQL, and then top it off with specialized stores as requirements dictate.
Common patterns:
- PostgreSQL/MySQL: transactional consistency, strong indexing, relational integrity
- MongoDB: flexible document models, rapid iteration for certain domains (use carefully with data consistency expectations)
- Redis: caching, rate limiting, session storage, queues (depending on architecture)
- Elasticsearch/OpenSearch: full-text search, faceted search, analytics-like querying (separate from your primary DB)
Design is good if it conforms to the shape of your data and the way you are accessing it. It also contains backup/restore testing, retention policies, and performance budgets.
Architecture Patterns (Monolith, Modular Monolith, Microservices)
Architecture should reflect your product stage and team size—not a theoretical end state. While microservices may be helpful at scale, they don't come without their own challenges and operational requirements such as service discovery, distributed tracing, deployment coordination, and data consistency.
A pragmatic progression:
- Monolith (early MVP): fastest iteration, simplest operations
- Modular monolith (growth): clearer boundaries, fewer accidental couplings
- Microservices (later): for when teams and scaling needs justify distributed complexity
When a vendor suggests microservices from day one, ask them how it addresses a problem today, and what it costs you in terms of DevOps, testing and debugging.
Hosting & Cloud (AWS/Azure/GCP) + Containers (Docker/Kubernetes)
Cloud choice is more often based on organizational preference, existing contracts, and talent.The bigger decision is usually how much you want to operate yourself.
Common deployment options:
- Managed PaaS promises faster ops with fewer knobs, like AWS Elastic Beanstalk, Azure App Service, and Google App Engine.
- Containers (Docker) on managed container services (ECS/Fargate, AKS, GKE) gives good balance of control and manageability
- Kubernetes is powerful, but adds complexity; best when you have strong platform skills or clear requirements that justify it
Ask vendors how they will implement environment parity, secrets, scaling policies, and disaster recovery. A production backend is more than “it runs.”
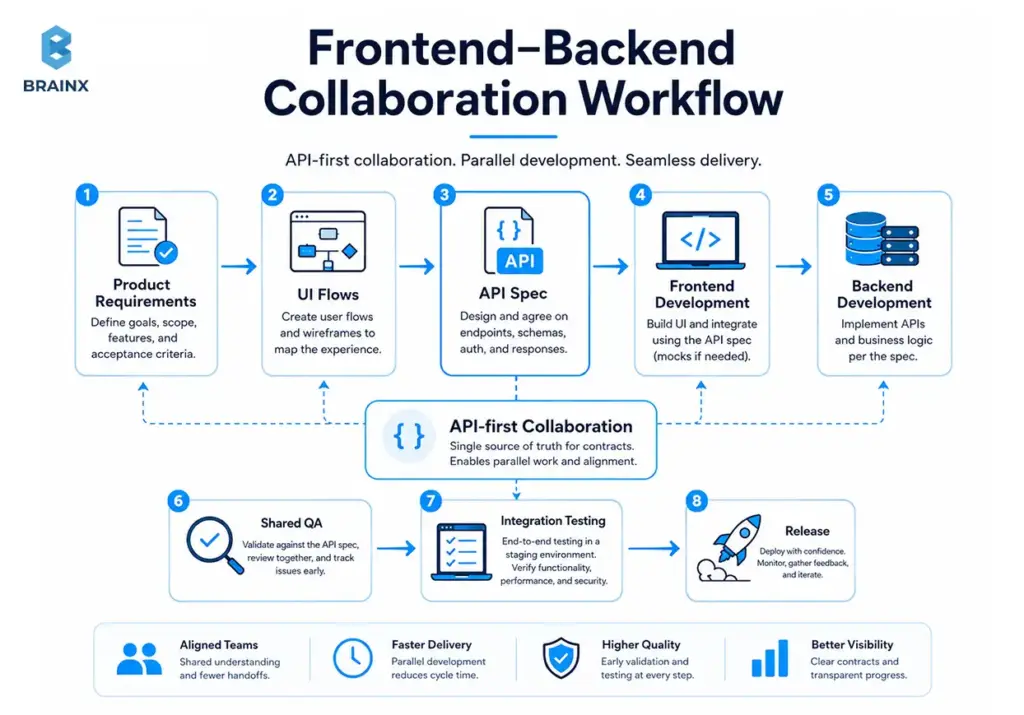
Frontend and Backend App Development: How the Teams Collaborate
Even with a single vendor, the backend and frontend must collaborate intentionally. With frontend and backend app development, misalignment usually appears as broken flows, inconsistent error handling, and late-stage rework.
A dependable collaboration workflow looks like this:
- API-first planning: endpoints and payloads designed alongside UI flows
- Shared definitions: error codes, validation rules, pagination, sorting
- Mock servers or schema-based stubs so frontend can move early
- Contract tests to prevent breaking changes
- Integrated QA scenarios (not separate “FE QA” and “BE QA”)
If you split vendors, enforce a written contract: API schema ownership, change control, and a release calendar.
Future Trends and Developments in Backend Development
Backend development is moving toward more standardized, platform-driven operations. Instead of asking every product team to manage infrastructure details directly, more organizations are adopting platform engineering models that give developers safer, more reusable paths to deploy and operate services. At the same time, cloud native practices have become mainstream, which means backend decisions are increasingly shaped by portability, observability, and operational consistency rather than just framework preference.
Another clear trend is the tighter connection between backend systems and AI-enabled workflows. That does not just mean adding AI features to products. It also means backend teams are thinking more carefully about inference workloads, workload isolation, API governance, and the cost and reliability impact of AI-powered services in production. AI tools are also improving developer productivity, but current research shows they still need strong testing, stable priorities, and disciplined delivery practices to avoid hurting software stability.
Security and API governance are also becoming more important, not less. Modern backends rely heavily on APIs and third-party services, which makes authorization, resource consumption controls, inventory management, and safe external API consumption more critical in future architectures. In practice, this means the strongest backend teams will increasingly win through cleaner contracts, stronger observability, better platform guardrails, and more deliberate operational design rather than through “trendier” stacks alone.
Backend Cost Explained: What a Backend App Development Company Will Quote
When you request estimates, a backend app development company typically prices the work based on scope, risk, and the level of production readiness you need. Backend costs spike when requirements include complex permissions, heavy integrations, high availability, and compliance obligations.
The best way to budget is to separate “build cost” from “run cost.” You’ll pay to implement the backend, then you’ll continue paying for cloud resources, monitoring tooling, third-party APIs, and support.
To avoid sticker shock, push vendors to translate features into engineering effort drivers: data migrations, concurrency, reliability targets, and operational readiness. Those details are where estimates become realistic.
Pricing Models (Fixed Price vs Time & Materials vs Dedicated Team)
Different models allocate risk differently. There’s no universally “cheapest” model—only what fits your uncertainty level.
- Fixed Price
Works well when scope is stable and defined explicitly (clear acceptance criteria with few unknowns). Risk: change requests become expensive as vendors might optimize for scope containment instead of outcomes. - Time & Materials (T&M)
Best when requirements keep evolving, or when you want to iterate based on learning. Risk: Product ownership is essential and needs to be reported clearly to prevent drifting away from the product. - Dedicated Team
You hire a persistent squad (backend + QA + DevOps + PM). Best for ongoing roadmaps and scaling products. Risk: you must give direction and prioritization, same as an internal team.
Inquire from vendors about their choice of model and why.
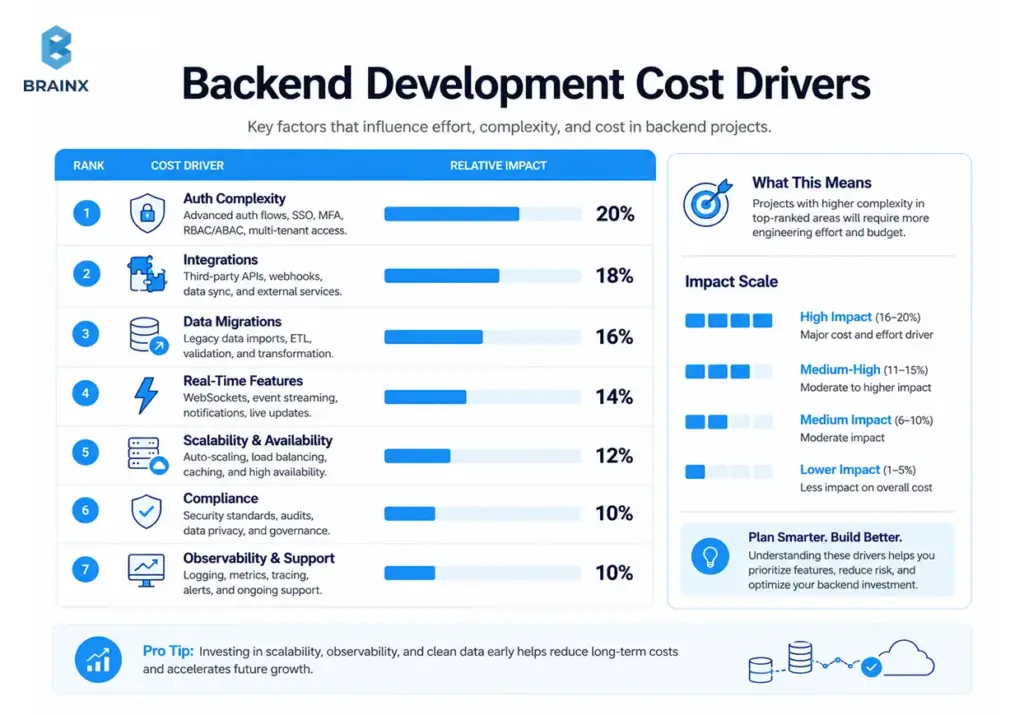
Key Cost Drivers Unique to Backend
The complexity of permissions, data evolution, integrations, and the reliability expectations increase with the amount of work done in the backend. Here are the drivers that tend to have the greatest impact on estimates:
- Auth complexity: simple login vs multi-tenant RBAC vs SSO with enterprise IdPs
- Integrations count + complexity: webhooks, retries, reconciliation, sandbox vs production differences
- Data model + migrations: zero downtime migrations, evolving schemas, and backfills.
- Real-time features: WebSockets, pub/sub, presence, live updates, fanout
- Scalability/availability requirements: multi-AZ, autoscaling, load testing, DR strategy
- Compliance needs: SOC 2, HIPAA, GDPR, audit logs, retention policies
- Observability & on-call readiness: dashboards, alerts, runbooks, incident response workflows
If two vendors quote wildly different numbers, ask them to walk you through these drivers line-by-line. The cheaper quote often assumes less production readiness.
Typical Timeline Ranges (MVP vs Production vs Enterprise)
Timelines are primarily a function of scope clarity and non-functional requirements (NFRs). A realistic vendor will propose a discovery phase to reduce unknowns before locking dates.
Typical ranges (directional, not universal):
- MVP backend: 6–12 weeks for a focused scope with basic auth, core APIs, and a straightforward data model
- Production-ready v1: 3–6 months when adding hardened security, CI/CD, observability, and multiple integrations
- Enterprise-grade: 6–12+ months for multi-tenant scale, SSO/RBAC depth, compliance controls, and high availability
Your timeline also depends on decision speed: access to stakeholders, clear priorities, and responsiveness to technical questions.
Hidden Costs to Plan For (Cloud, Monitoring, Third-Party APIs, Support)
Even a well-estimated build can feel “over budget” if you ignore operating costs. Plan for:
- Cloud spend: environments, databases, caches, egress, backups
- Monitoring/logging: APM tools, log retention, alerting services
- Third-party APIs: usage-based pricing (maps, SMS, email, AI services)
- Security tooling: WAF, vulnerability scanning, secrets management
- Support: on-call coverage, incident response, maintenance cycles
A good vendor will help you estimate TCO (total cost of ownership) and set practical budgets per environment.
How to Reduce Backend Development Cost
Cost reduction works best when it’s actually risk reduction: fewer unknowns, smaller release batches, and less rework. The goal isn’t to cut corners on security or reliability; it’s to spend effort where it matters.
Use the strategies below to reduce cost without accumulating hidden debt. Each one also improves estimation accuracy, which is a major lever in controlling spend.
When vendors resist these steps, it’s often a sign they’re optimizing for short-term output rather than long-term maintainability.
Build MVP First
An MVP backend should prove the core workflow and data model with minimal operational overhead—while still being safe to run.
Practical MVP tactics:
- Implement only the permissions needed for v1 roles
- Limit integrations to one payment provider or one messaging channel
- Use managed services (managed Postgres, managed queues) to reduce ops burden
- Prioritize stable API contracts for the core flows
A well-shaped MVP also creates a clean path to production hardening later, instead of requiring a rewrite.
Avoid Over-Engineering
Over-engineering is expensive because it creates complexity you must maintain. Common examples: microservices too early, elaborate event-driven setups for simple workflows, and premature multi-region designs.
Cost-saving questions to ask:
- What scale do we actually need in the next 6–12 months?
- Can we meet current performance targets with simpler architecture?
- What do we lose by deferring this complexity?
If your vendor can’t articulate the operational cost of their architecture choices, push back.
Choose Scalable Architecture Early
This doesn’t mean “build microservices early.” It means choose an architecture that can scale without dramatic rewrites:
- Clear module boundaries and domain separation
- Database schema designed for growth (and migrations designed for safety)
- Stateless services where possible
- Good observability hooks from day one
This approach makes scaling incremental: optimize queries, add caching, split modules, then split services only when necessary.
Reuse Open-Source Frameworks
Open-source frameworks reduce build time, but only if they’re used intentionally:
- Prefer widely adopted libraries with active maintenance
- Avoid niche dependencies that lock you into a single maintainer
- Ensure licensing is compatible with your business
Reusable components that often save real money:
- Auth libraries and OIDC clients
- Migration tooling
- Background job frameworks
- API documentation generators (OpenAPI tooling)
The vendor should also commit to dependency update practices to reduce security risk.
Proper Documentation
Documentation is cost control because it reduces onboarding time and prevents institutional knowledge from living only in Slack.
Minimum documentation that pays off quickly:
- Environment setup + local run instructions
- API docs and example requests
- Architecture overview and data model notes
- Deployment steps and rollback procedures
- Runbooks for common incidents
This also makes vendor transitions less risky if you ever change teams.
How to Choose the Right Backend App Development Company
Selecting a backend app development company is less about a portfolio and more about evidence of engineering maturity: security practices, testing discipline, operational readiness, and clarity in estimation.
Use a scorecard approach so your evaluation is repeatable and defensible—especially in enterprises where procurement and risk teams are involved.
Below is a practical framework you can use in vendor calls and proposal reviews. The goal is to surface capability gaps before they become delivery problems.
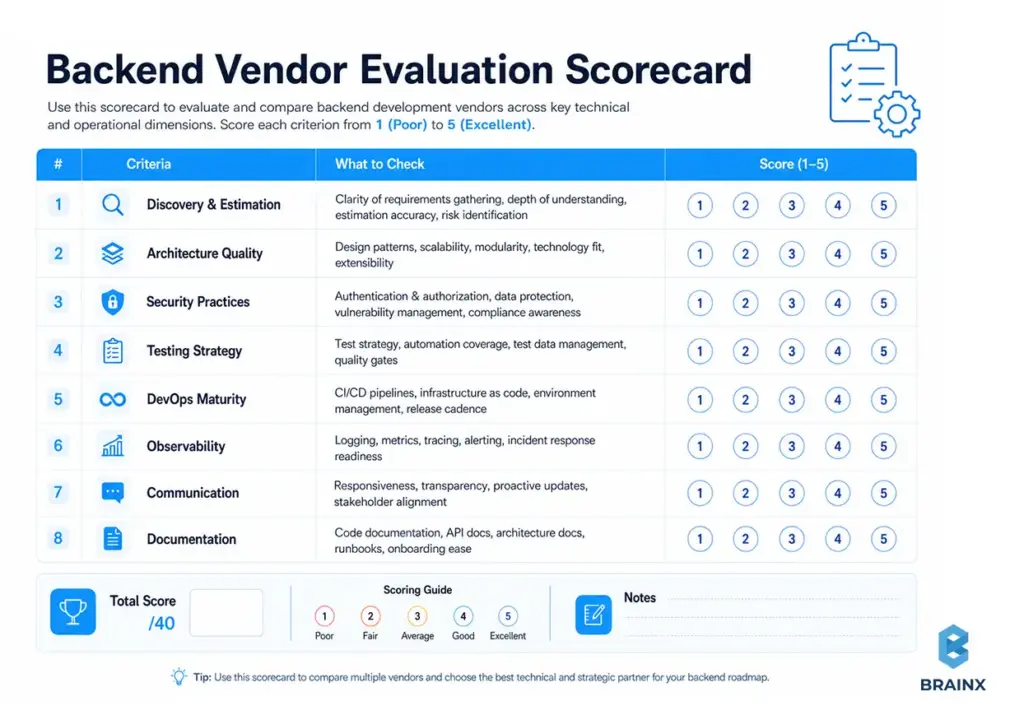
Must-Ask Questions (Discovery, Architecture, Security, DevOps)
Use these questions to reveal how the vendor thinks—and whether they’ve operated production systems, not just built demos.
- How do you capture non-functional requirements (latency, uptime, RPO/RTO, compliance)?
- What does your discovery phase produce (architecture, API spec, estimates, risk log)?
- How do you design and version APIs to prevent breaking clients?
- What’s your database migration strategy for zero-downtime releases?
- How do you handle RBAC/SSO requirements in multi-tenant systems?
- What security standards do you follow (OWASP, secure SDLC practices)?
- What automated tests do you require before merging to main?
- How do you do performance testing, and what metrics do you report?
- What’s in your CI/CD pipeline (SAST/DAST, dependency scanning, approvals)?
- Which environments do you set up, and how do you keep them consistent?
- What observability stack do you ship with (logs/metrics/traces, alerting)?
- How do you handle incidents (on-call, escalation, postmortems)?
- How do you estimate work, and how do you track variance?
- How do you manage scope changes without derailing timelines?
- What documentation do you deliver, and how do you keep it updated?
Strong vendors answer with specifics, examples, and artifacts—not generalities.
Proof to Look For (Case Studies, System Metrics, References)
Portfolios show UI screenshots; you need evidence the backend performs under real conditions.
Look for proof like:
- Case studies with measurable outcomes (latency improvements, uptime, deploy frequency)
- Architecture diagrams and system boundary explanations
- Redacted dashboards (APM metrics, error rates, queue depth, SLO adherence)
- References that can speak to reliability and post-launch support
- Evidence of secure practices (threat modeling, security reviews, audit logs)
If a vendor can’t talk about production metrics, ask whether they’ve run what they build.
Red Flags (Overpromising, No testing, No monitoring, Vague estimates)
These warning signs correlate strongly with cost overruns and unstable releases:
- Promises of “any feature in two weeks” without discovery
- No clear testing strategy beyond manual QA
- No mention of observability, alerting, or incident response
- Estimates with no breakdown (just a single number)
- “We’ll figure out security later” or vague compliance claims
- Heavy reliance on one senior engineer with no redundancy
- Refusal to define acceptance criteria or deliverables
A healthy vendor relationship is built on transparency and shared risk management.
Engagement Setup: Team Roles You Actually Need
Backend delivery is a team sport. The leanest effective team depends on scope, but most successful engagements include:
- Backend engineers (2–4): APIs, services, data layer, integrations
- Tech lead/architect (part-time or full-time): architecture decisions, reviews, risk management
- DevOps/SRE (part-time early, more later): CI/CD, infra, observability, reliability
- QA engineer: automation strategy, integration/performance testing, release validation
- Product/Project manager: scope control, stakeholder alignment, reporting
If the vendor proposes “one full-stack dev can do it all,” push for realism—especially if production reliability matters.
Common Challenges in App Backend Development (and How to Avoid Them)
Most backend failures aren’t mysterious; they’re predictable outcomes of rushed decisions and missing operational rigor. In app backend development, the biggest risks are usually performance surprises, security debt, brittle APIs, and lack of visibility in production.
A good plan treats these as engineering constraints from day one. You don’t need enterprise-grade everything for an MVP, but you do need a clear path to get there.
Below are common challenges and practical mitigations you can bake into scope, acceptance criteria, and vendor selection.
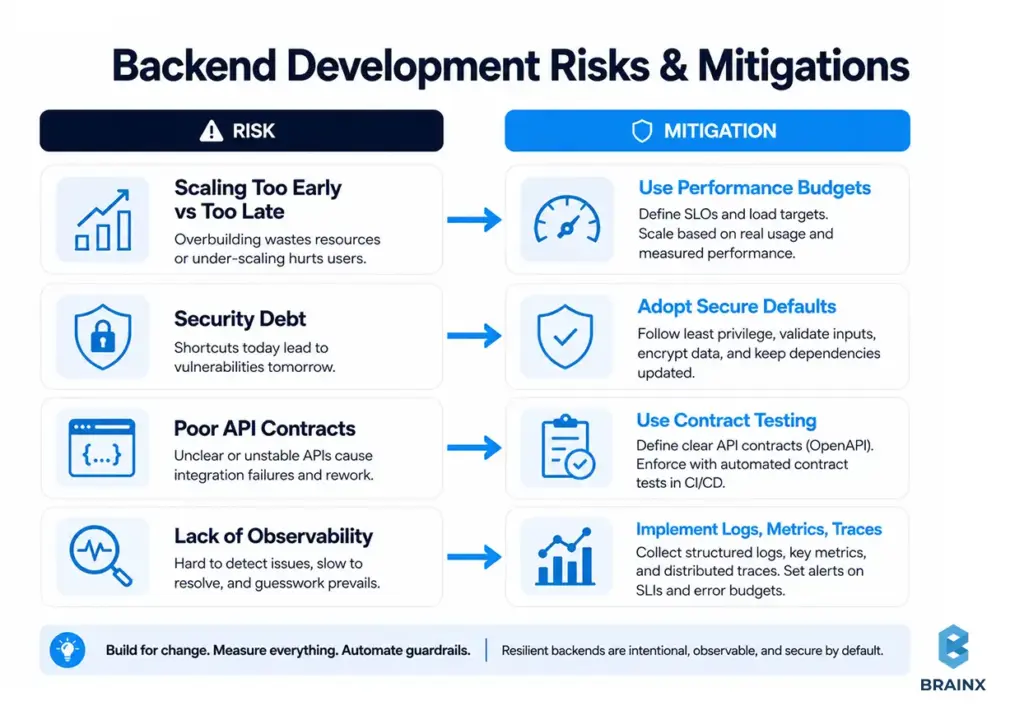
Scaling Too Early vs Too Late
Scaling too early leads to overbuilt systems with slow delivery. Scaling too late leads to outages, hotfix chaos, and emergency rewrites.
Avoid both by:
- Setting explicit performance budgets (p95 latency, throughput) for v1
- Load testing critical flows before major launches
- Designing modular boundaries so you can scale parts independently
- Planning a scaling roadmap (cache → read replicas → service split), not a leap
The goal is progressive scaling—measured, not speculative.
Security Debt and Compliance Gaps
Security debt grows silently: hardcoded secrets, unclear permissions, weak audit logs, and inconsistent validation. Compliance gaps show up later as sales blockers (enterprise deals) or regulatory risk.
Mitigations:
- Implement RBAC/tenant isolation correctly early
- Centralize auth and authorization checks (don’t scatter logic)
- Add audit logs for critical actions (and protect them from tampering)
- Automate dependency scanning and patch routines
- Document data retention and deletion flows (GDPR-like requirements)
If you expect enterprise customers, build a compliance runway early—without fully “doing SOC 2” on day one.
Poor API Contracts and Slow Iteration
Brittle APIs cause slow iteration because every change risks breaking clients. The cost shows up as coordination tax across mobile/web, QA, and support.
Mitigations:
- Use OpenAPI schemas and enforce them in CI
- Standardize error formats and validation responses
- Adopt backward-compatible change rules (additive changes first)
- Use contract tests for key clients or shared SDKs
A stable API contract is one of the strongest accelerators for product teams.
Lack of Observability (You Can’t Fix What You Can’t See)
Without logs, metrics, and traces, teams guess. Guessing leads to slow incident resolution and fragile fixes.
Mitigations:
- Define “golden signals” (latency, traffic, errors, saturation)
- Implement structured logging with correlation IDs
- Add tracing for critical workflows (checkout, onboarding, sync jobs)
- Create actionable alerts (avoid noisy alert storms)
- Maintain runbooks for common incidents and recovery steps
Observability isn’t optional once real users depend on you.
A Practical Implementation Plan (From Idea to Launch)
A solid delivery plan reduces risk and improves estimated accuracy. It aligns product requirements with technical constraints and ensures production readiness is built in—not bolted on.
This implementation plan mirrors how mature teams deliver: discovery first, architecture decisions early, incremental delivery, automated testing, and operational readiness before launch.
If you’re working with a vendor, these steps also make responsibilities clear: what they deliver, what you review, and when you can make scope decisions with real information.
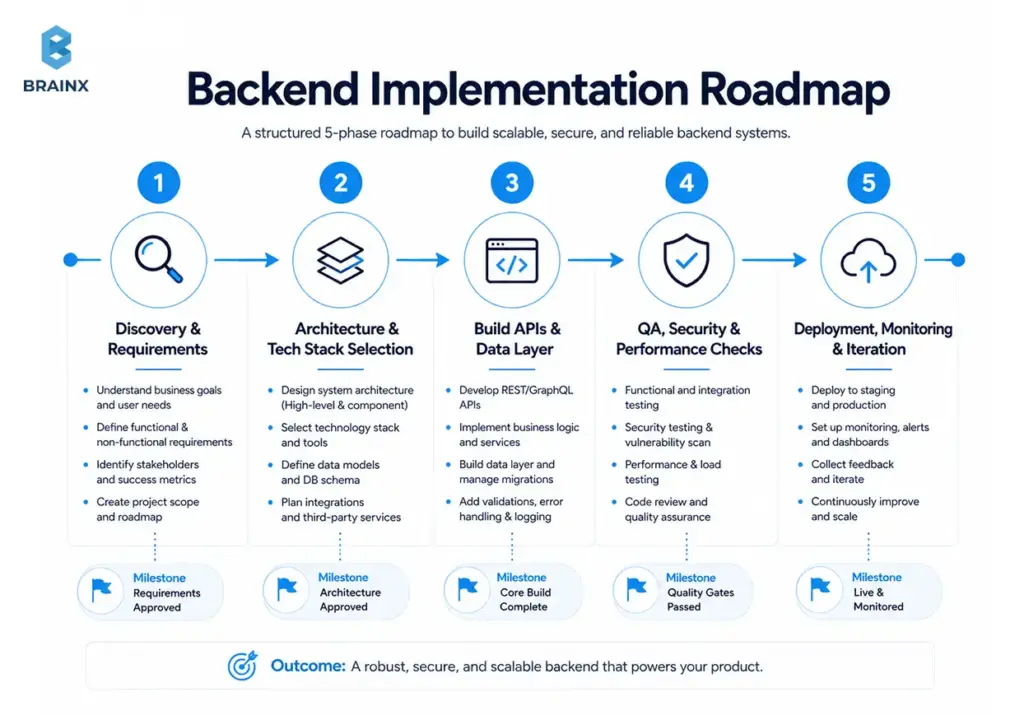
Step 1 — Discovery & Requirements (NFRs Included)
Discovery should produce clarity, not slide decks. Minimum outputs:
- User flows and system actors (clients, admins, partners)
- Data entities and lifecycle (create/update/delete, retention)
- Non-functional requirements: latency targets, uptime expectations, compliance needs
- Integration list and constraints (webhooks, rate limits, sandbox access)
- Risk log (unknowns + how to validate them)
This is also where you decide what “production-ready” means for v1.
Step 2 — Architecture & Tech Stack Selection
Architecture is about trade-offs. A good team will propose options and explain consequences.
Decisions to finalize:
- Service boundaries (start simple; define modules)
- Data strategy (primary DB + caching/search needs)
- Auth approach (JWT, OIDC, SSO readiness)
- Deployment strategy and environments
- Observability baseline (what you will measure from day one)
You should also agree on core conventions: error handling, logging format, API patterns, and versioning.
Step 3 — Build APIs, Data Layer, and Core Services
Execution should be incremental and demonstrable:
- Implement core domain services and data model
- Deliver API endpoints with tests and documentation
- Build integration adapters (payments, messaging) with sandbox validation
- Add background workers for async tasks (emails, webhooks, processing jobs)
- Enforce coding standards and review gates
Prefer vertical slices: ship one complete workflow end-to-end, then expand.
Step 4 — QA, Security Testing, and Performance Checks
Before launch, validate more than “happy paths”:
- Integration tests for critical flows and edge cases
- Contract tests for key API consumers
- Security checks: auth bypass attempts, input validation, dependency scans
- Performance checks: load tests for top endpoints and concurrency behaviors
- Failure mode testing: timeouts, retries, queue backlogs, third-party outages
This step is where many projects discover hidden requirements. Better here than after launch.
Step 5 — Deployment, Monitoring, and Iteration
Launch readiness is operational readiness:
- CI/CD pipelines with rollback strategy
- Monitoring dashboards and alert thresholds
- Log retention and incident response plan
- Runbooks for common failures
- Post-launch iteration plan (bugfix cycles, performance tuning, feature roadmap)
A smooth launch is not luck; it’s the result of deliberate preparation.
How BrainX Helps with Your Backend App Development Company Needs?
If you’re looking for a backend app development company that can design, build, and run production-grade backends (not just deliver endpoints), BrainX Technologies helps teams ship with clarity and operational maturity.
We typically support clients across:
- Discovery and estimation: requirements, NFRs, architecture options, risk mapping, and phased roadmaps
- API and service engineering: REST/GraphQL, background jobs, event-driven patterns where justified
- Security-first backend delivery: auth, RBAC/SSO readiness, secure defaults, and hardening aligned to recognized standards
- DevOps and reliability: CI/CD pipelines, Infrastructure as Code, observability (logs/metrics/traces), and post-launch support options
- Scalable evolution: modular architectures that can grow without forcing microservices prematurely
If you want to validate scope and costs quickly, we can run a focused discovery and provide an estimate with clear assumptions, deliverables, and a phased plan.
Real-World Backend Examples and Case Studies
Real backend complexity usually shows up in the operating details, not the UI. A SaaS platform may need tenant-aware permissions, audit trails, and SSO before it can sell into larger accounts. A marketplace may need payment workflows, reconciliation logic, refunds, notifications, and protection against duplicate webhook events. A mobile app may look simple on the surface but still depend on secure auth, sync logic, rate limiting, and background processing to work reliably in production.
That is why strong backend delivery is best evaluated through outcomes, not just features shipped. In practice, good backend work often looks like faster release cycles, fewer production incidents, cleaner integrations, safer schema changes, and better visibility into system behavior after launch. Those are the signals that the backend is not only functional, but also maintainable under real usage.
For buyers, the lesson is simple: case studies matter most when they explain what changed operationally. Instead of looking only for screenshots or generic success claims, look for examples that show how a team handled permissions, integrations, uptime expectations, deployment safety, or scaling pressure. That is where backend quality becomes visible.
Conclusion
Choosing a backend partner is ultimately about reducing long-term risk: stable APIs, secure access control, data integrity, and production readiness you can operate confidently. The best approach is to scope backend deliverables clearly, pick a stack that matches your constraints, and budget for the real drivers—integrations, auth depth, observability, and reliability targets.
If you’re evaluating a backend app development company, use the checklists and questions above to compare proposals on engineering maturity, not just price. When you’re ready, schedule a scoping session to turn your requirements into a phased plan and an estimate you can trust.
FAQs From A Backend App Development Company
What does a backend app development company typically deliver?
A backend app development company typically delivers production-ready server-side functionality, including APIs, business logic, database design, and integration layers. You should also expect supporting assets like API documentation, migration scripts, CI/CD setup guidance, and baseline monitoring/alerting. For mature engagements, deliverables often include infrastructure as code, runbooks, and security hardening steps. The best vendors define these outputs explicitly in the proposal so there’s no ambiguity at handoff.
How much do backend app development services cost for an MVP?
Costs for backend app development services vary mainly by scope, integration count, and security requirements. A simple MVP backend with basic auth, a small data model, and a limited set of APIs can be far less expensive than an MVP that includes SSO, complex RBAC, real-time features, and multiple third-party integrations. Vendors also price differently depending on whether you choose fixed price, time & materials, or a dedicated team. The most reliable way to budget is a short discovery phase that converts your MVP into a clearly estimated scope with assumptions.
What’s included in app backend development beyond APIs and databases?
App backend development often includes authentication and authorization, background job processing, caching, and integration handling (webhooks, retries, idempotency). It also commonly includes deployment automation (CI/CD), environment configuration, and observability (logs, metrics, traces) so the system can be operated safely. For regulated or enterprise contexts, you may also need audit logging, retention policies, and security controls aligned to compliance requirements. In other words, “beyond APIs and databases” is usually where production reliability lives.
Should I hire one team for frontend and backend app development or split vendors?
If you need tight coordination and fast iteration, one team for frontend and backend app development can reduce handoffs and shorten feedback loops. A single team can design APIs around UI flows, align error handling, and run integrated testing earlier. Splitting vendors can work when you have strong internal technical ownership and a clear API contract process (schemas, contract tests, versioning rules). If you split, define ownership boundaries up front—especially around API specs, QA responsibility, and release sequencing.
Which backend tech stack is best for scaling (Node vs Python vs Java vs .NET)?
There’s no single best stack for scaling; scaling success depends more on architecture, data design, and operational maturity than on language choice. Node.js and Python can scale very well for many SaaS products when paired with good caching, database design, and horizontal scaling. Java and .NET are common in enterprise systems due to mature tooling, strong performance profiles, and governance alignment. The right answer depends on your team skills, compliance needs, and what you can operate reliably over time.
How do I evaluate security and compliance readiness in a backend vendor?
Ask for specifics: how they implement RBAC/SSO, how they manage secrets, and what secure SDLC practices they use (dependency scanning, code review gates, security testing). Request references or examples of audit logs, threat modeling practices, and how they handle incident response. A credible vendor can also describe how they align to OWASP recommendations and how they support compliance roadmaps like SOC 2 or HIPAA (without hand-waving). Finally, look for operational evidence: monitoring, alerting, and runbooks—security is inseparable from reliability in production.